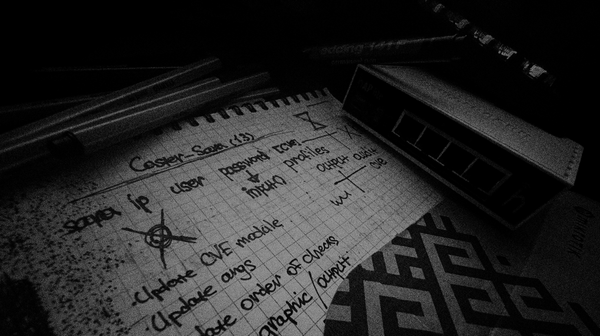
CSTR:JNOS-SEC:082025 [TEASER]
![CSTR:JNOS-SEC:082025 [TEASER]](/content/images/size/w1200/2025/08/IMG_2800.JPG)
![CSTR:JNOS-SEC:082025 [TEASER]](/content/images/size/w1200/2025/08/IMG_2800.JPG)

A deep technical dive into how MITM attacks actually work in Ethernet, IPv4, and IPv6 networks from ARP and DHCP to IPv6 RA, DNS, and FHRP spoofing.
I have released a new version v1.3.0 of my tool Sara, a RouterOS configuration analyzer.

This is research on detecting attacks on Kerberos using traffic analysis.
![Noir: How to Protect Juniper Networks [Demo]](/content/images/size/w600/2025/10/noirvideocover-1.png)
A short demo of Noir, a tool that analyzes Juniper JunOS configurations for vulnerabilities, weak access controls, and misconfigurations.