
Articles
Intercept: How MITM attacks work in Ethernet, IPv4 & IPv6
A deep technical dive into how MITM attacks actually work in Ethernet, IPv4, and IPv6 networks from ARP and DHCP to IPv6 RA, DNS, and FHRP spoofing.

Articles
A deep technical dive into how MITM attacks actually work in Ethernet, IPv4, and IPv6 networks from ARP and DHCP to IPv6 RA, DNS, and FHRP spoofing.
Tool
I have released a new version v1.3.0 of my tool Sara, a RouterOS configuration analyzer.

Articles
This is research on detecting attacks on Kerberos using traffic analysis.
![Noir: How to Protect Juniper Networks [Demo]](/content/images/size/w600/2025/10/noirvideocover-1.png)
Video
A short demo of Noir, a tool that analyzes Juniper JunOS configurations for vulnerabilities, weak access controls, and misconfigurations.
Tool
Release of JunOS Security Inspector

Articles
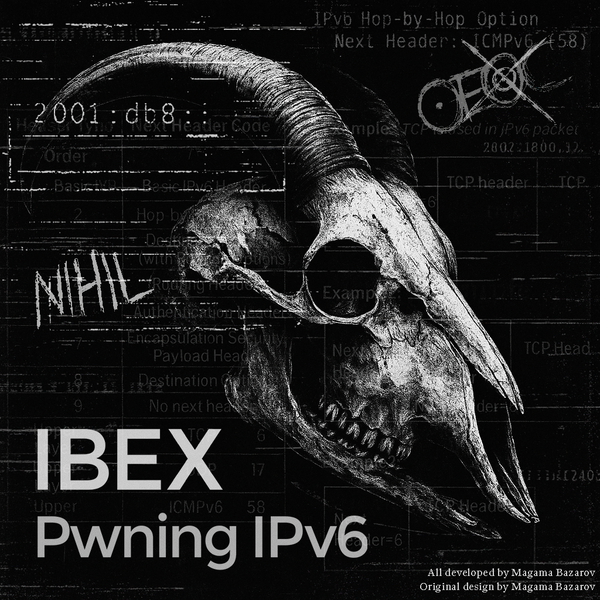
IPv6 often remains active in corporate networks. In this article, I will discuss attacks on IPv6 and detection methods.
![CSTR:LGLSSIPV6:ATK [TEASER]](/content/images/size/w600/2025/08/CSTRLGLSSOFFENSIVEREDUX.JPG)
Teasers
On September 1, I will publish an article on attacks on IPv6. Don't miss it!
![CSTR:JNOS-SEC:082025 [TEASER]](/content/images/size/w600/2025/08/IMG_2800.JPG)
Teasers
Tool
Interactive IPv6 toolkit for pentesting IPv6 networks.
![Seen It All: Detecting Active Directory Attacks with Suricata IDS [English Subtitles]](/content/images/size/w600/2025/08/castersiacover.jpg)
Video
Research on detecting attacks on Active Directory based on network traffic analysis.
Kali Linux
RouterOS Security Inspector performs configuration analysis for vulnerabilities and includes a CVE search function.

Articles
Pivoting is used in post-exploitation and has many methods, this article will talk about pivoting using Nebula.